KEY ADVANTAGES OF RutOS: SECURITY
#rutos, #security
Security risk tests are performed constantly on all Teltonika Networks devices, and all products are being periodically updated to eliminate any potential weaknesses and assure the highest level of safety. We have multiple features embedded into our RutOS oriented towards better defense against cybersecurity threats.
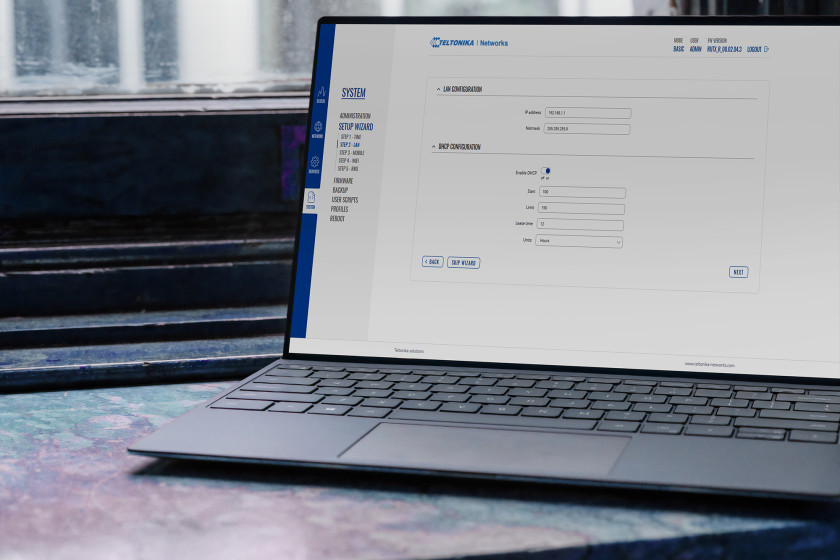
By default, our routers are configured to be maximally secured. We care about the safety of your solution from the moment our product leaves the production line. Although it is easy to use for users of all levels, we aim to protect against any possible threats. Therefore, we block all unnecessary accesses so that the functionality does not result in harm for less experienced customers.
PASSWORD MANAGEMENT
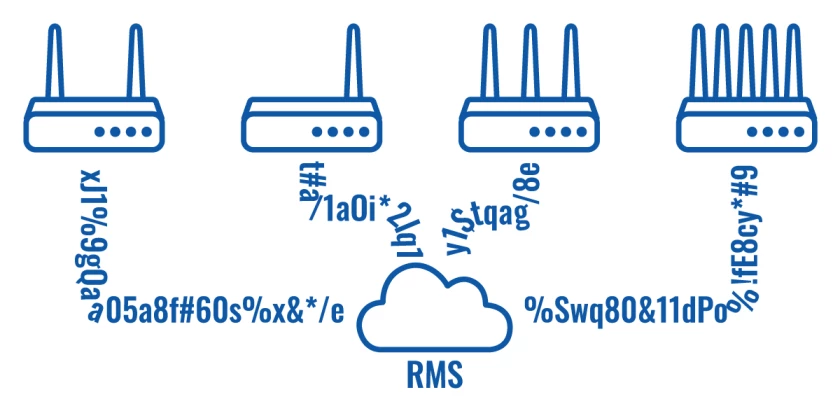
Our Web Interface, unlike a lot of ones by other manufacturers, requires a mandatory password change upon the initial setup process. An unbelievable amount of IoT solution breaches come from a simple weakness of using generic passwords for device access. Teltonika Networks products cannot be deployed before securing them. This is the first but essential step towards good password management practices. Using the RMS cloud platform allows our users to easily change or autogenerate secure passwords for an infinite number of devices within a few clicks. To add another layer of security, we implemented IP blocking whenever a wrong password is attempted for five times. This feature efficiently prevents from unwanted guests entering companies’ devices and systems remotely.
VPN & FIREWALL
A Virtual Private Network (VPN) is a method of connecting multiple private networks across the Internet. VPNs can serve to achieve many different goals, but some of its main purposes are:
- access between remote private networks;
- data encryption;
- anonymity when browsing the Internet.
It is not uncommon for the routers to offer one or another VPN service. However, RutOS stands out by the variety of VPN services available to our clients: OpenVPN, IPsec, GRE, PPTP, L2TP, Zerotier, DMPVPN, and SSTP. Another great and exclusive feature of RutOS is the possibility to generate TLS certificates to provide privacy and data integrity between two communicating computer applications. This tool enables for greater autonomy and control of your network as well as streamlines the setting up process.
For even more security, we have a set of preconfigured Firewall rules in RutOS. Although these rules can be customized with unlimited configuration options via Web UI, we made sure our products are safe to use for everyone from the very beginning, in case the routers are used by someone without in-depth network administration knowledge.

WEB FILTER
The Web Filter service provides you with a possibility to restrict which websites a user can visit on a local network. An administrator can upload Blacklists or Whitelists that are either blocking or allowing specific web addresses to be accessed. It is especially useful in Hotspots to limit data usage. Or let’s say in schools and enterprise settings to ensure that only the necessary IP addresses are reachable and the rest of the content is blocked.
SMS ACCESS SETTINGS
Since a variety of tasks can be carried out via SMS, we had to make sure only authorized devices can connect to the router. Therefore, by default, SMS commands will only work if both conditions are met: the SMS number and the router’s password are known to each other. There might be an extra layer of security, like authentication with a serial number to a specific phone number, or only accepting commands from a list of pre-approved numbers.
TCP DUMP
Let’s admit, network connectivity troubleshooting can be a real pain sometimes. TCP dump becomes life-savior in some situations. It is a program used to capture and decode packets moving through network interfaces. TCP dump is a very effective and comprehensive tool with a variety of options and filters, and fits perfectly for running on remote servers or routers.
These are just some of the security features available on RutOS that keep our clients’ networks safe. We continually improve and update our operating system to make sure it follows the highest-level security standards and ensures the prevention of any type of breaches. We also set-up safeguards for less experienced users, like mandatory password change or firewall rules, making sure our devices are safe to use from the very first moment they reach our client. This leads us to another property of RutOS we will discuss in the next chapter – ease of use.


